Zero-Knowledge Proof of Training Secures Federated Learning Consensus
ZKPoT uses zk-SNARKs to verify model contributions privately, eliminating the trade-off between decentralized AI privacy and consensus efficiency.
Zero-Knowledge Proof of Training Secures Private Federated Consensus
A novel Zero-Knowledge Proof of Training (ZKPoT) mechanism leverages zk-SNARKs to validate machine learning contributions privately, enabling a scalable, decentralized AI framework.
Adaptive Byzantine Agreement Reduces Communication Complexity Based on Actual Faults
A new synchronous protocol achieves adaptive word complexity in Byzantine Agreement, scaling communication with actual faults to unlock efficient, fault-tolerant consensus.
Horizontally Scalable zkSNARKs via Proof Aggregation Framework
This framework achieves horizontal zkSNARK scalability by distributing large computations for parallel proving, then aggregating results into a single succinct proof.
Secure Sharding Consensus Pattern Dramatically Scales Throughput with Optimized Overhead
Kronos introduces a buffer-based sharding consensus pattern, provably achieving cross-shard atomicity and $12times$ throughput for next-generation scalable architectures.
New Vector Commitment Achieves Asymptotically Optimal Sublinear Stateless Client Updates


Researchers construct a dynamic Vector Commitment scheme achieving asymptotically optimal sublinear complexity, fundamentally enabling truly efficient stateless blockchain clients.
New Asynchronous BFT Consensus Achieves Throughput-Oblivious Latency


This protocol overcomes the FLP barrier, delivering a practical asynchronous BFT consensus that maintains minimum latency regardless of network load.
Zero-Knowledge Proof of Training Secures Private Decentralized AI Consensus
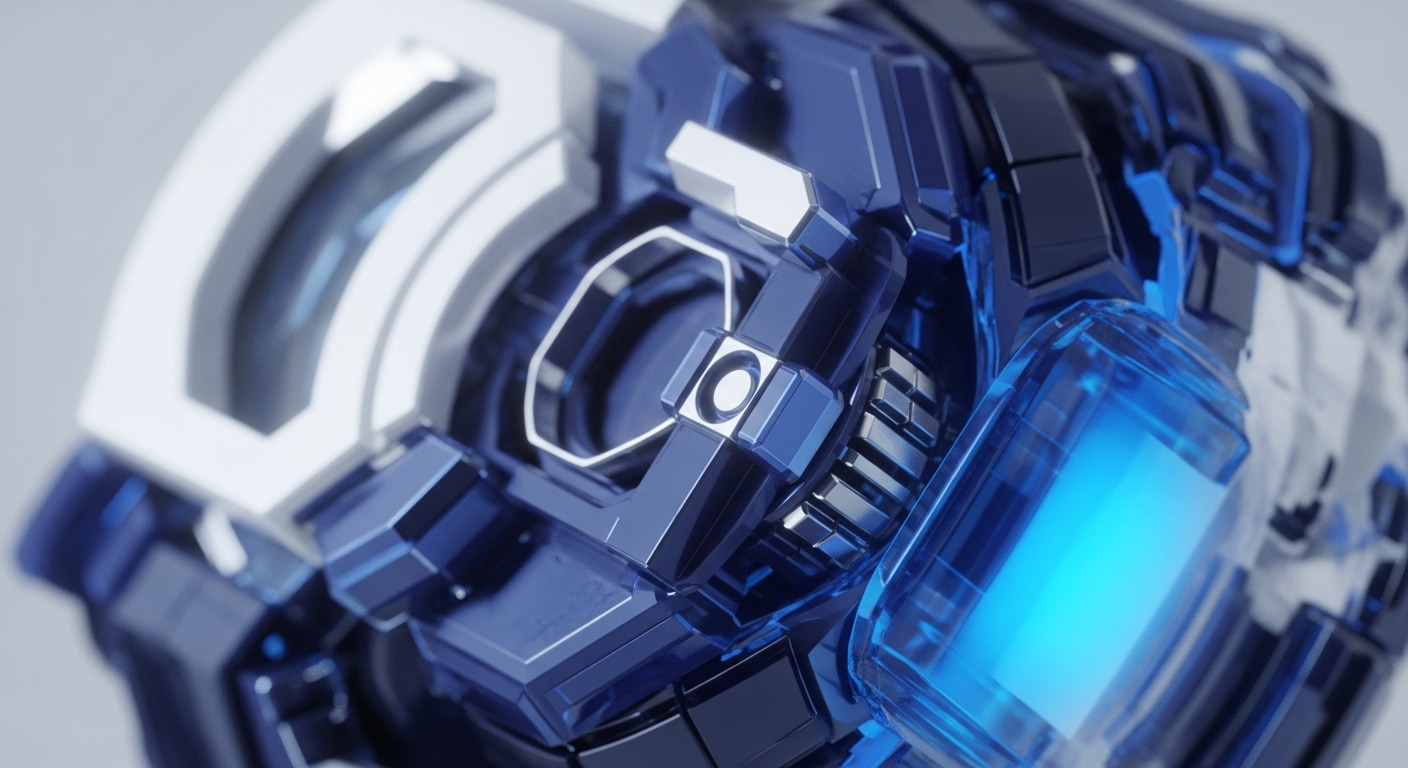
ZKPoT, a novel zk-SNARK-based consensus, cryptographically validates decentralized AI model contributions, eliminating privacy risks and scaling efficiency.
Formally Synthesizing Secure Distributed Systems from Centralized Programs


This research unifies simulation-based security with compiler techniques to automatically generate provably secure distributed cryptographic applications.