Adaptive Byzantine Agreement Achieves Optimal Communication Complexity
This protocol dynamically scales Byzantine Agreement communication cost with actual faults, unlocking optimal efficiency for large decentralized networks.
Transparent Polynomial Commitment Achieves Succinct Proofs without Trusted Setup
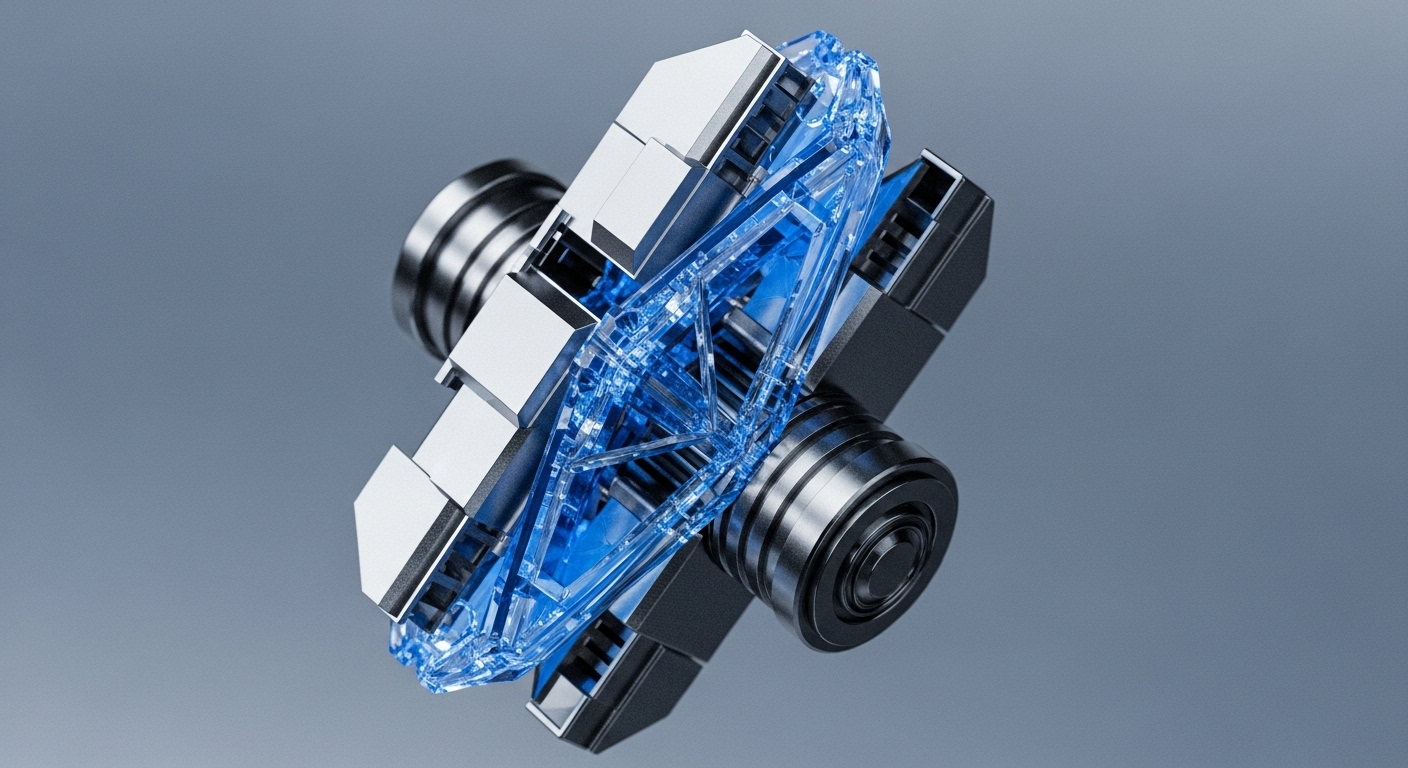
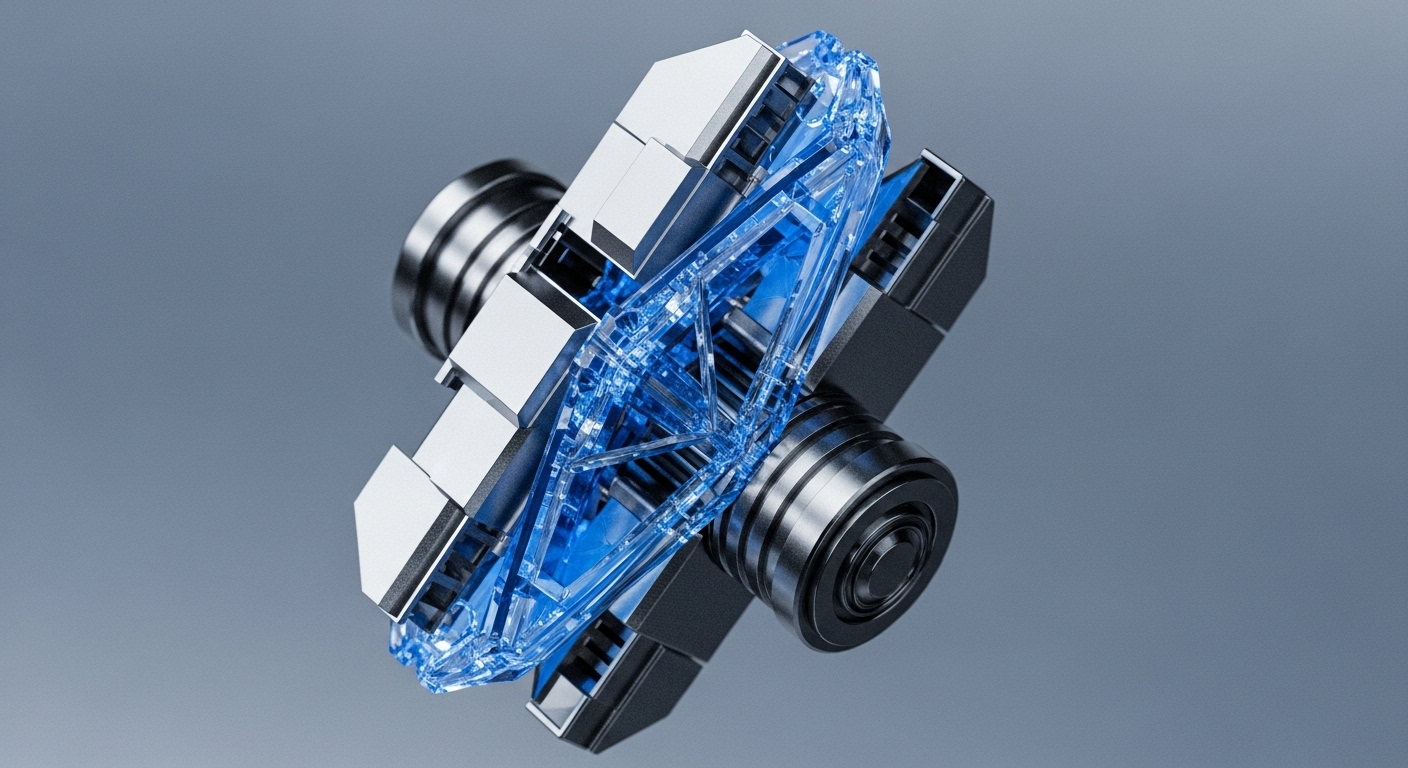
A novel polynomial commitment scheme achieves cryptographic transparency and logarithmic verification, eliminating the reliance on a trusted setup for scalable zero-knowledge proofs.
Linear-Time Zero-Knowledge Provers Unlock Universal Verifiable Computation
A linear-time ZKP prover mechanism achieves optimal computational efficiency, fundamentally enabling scalable, trustless verification for all decentralized applications.
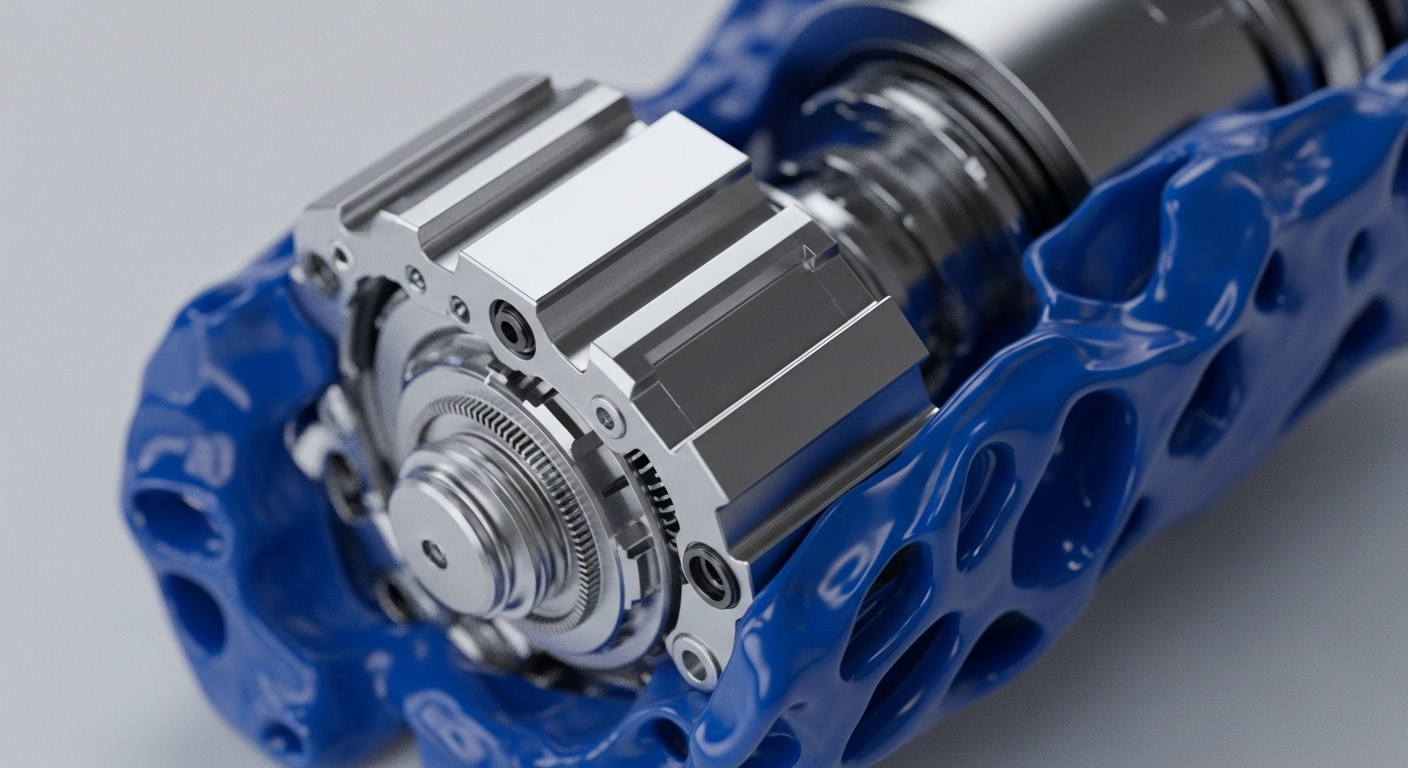
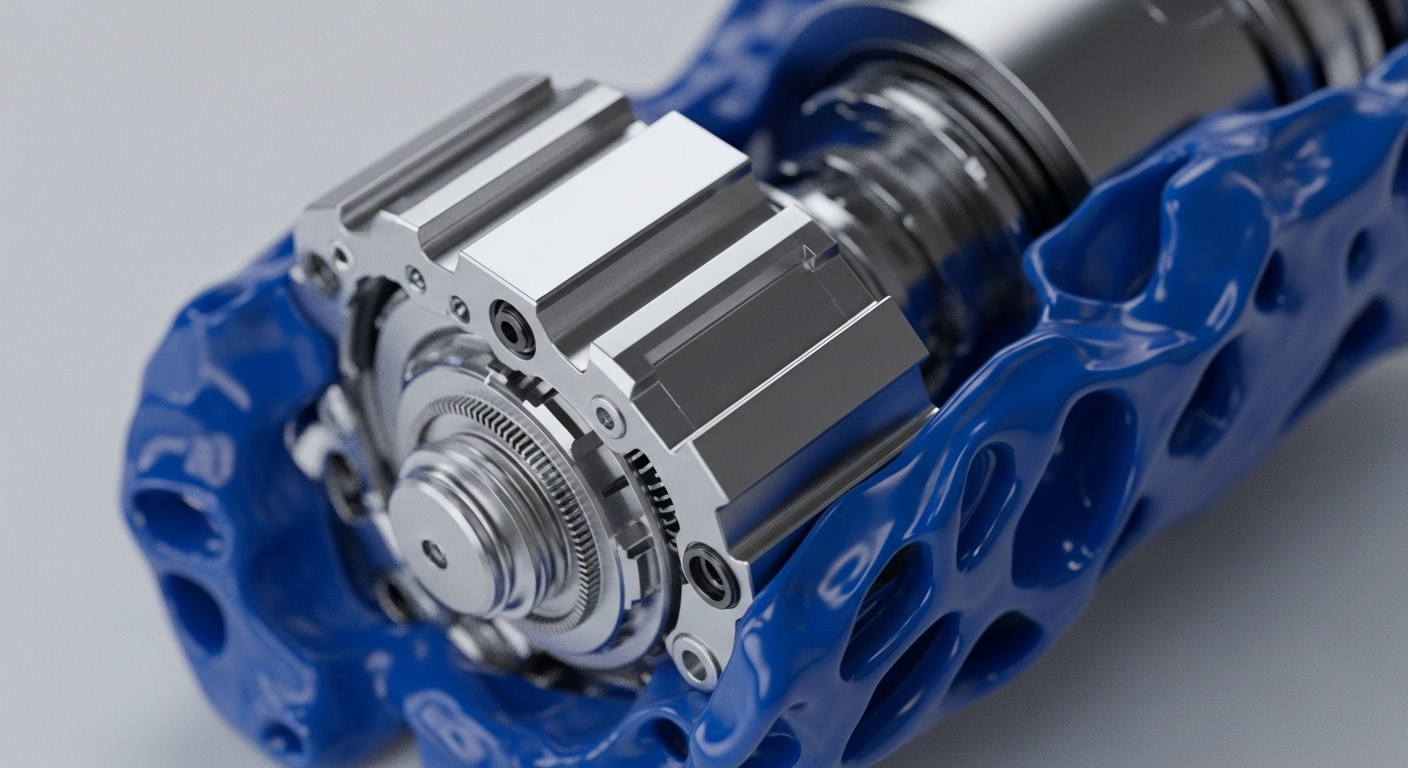
Distributed Service Architecture Unifies Threshold Cryptography Schemes for Reliable Deployment
A new distributed service architecture provides a unified, language-agnostic framework to integrate and accurately benchmark threshold cryptography, accelerating distributed trust applications.
Proof-of-Useful-Work Decouples Consensus Security from Wasted Energy
A novel Doubly Parallel Local Search mechanism transforms PoW's wasted energy into a decentralized, provably secure combinatorial optimization engine.
Signature-Free Asynchronous Byzantine Agreement Achieves Optimal Communication Complexity
This new signature-free asynchronous Byzantine agreement protocol achieves the theoretical optimal communication complexity for unauthenticated consensus.
Mechanism Design Secures Leaderless Protocol Block Producer Incentives


A new extensive-form game model and the FPA-EQ mechanism solve block producer incentive misalignment in leaderless consensus protocols.
Zero-Knowledge Proof of Training Secures Decentralized Machine Learning Integrity
The Zero-Knowledge Proof of Training (ZKPoT) mechanism leverages zk-SNARKs to validate model accuracy without exposing private data, enabling provably secure on-chain AI.
High-Throughput Threshold FHE Decryption Unlocks Practical Universally Composable MPC


A new Universally Composable Threshold FHE decryption protocol achieves high throughput via an offline-online structure, enabling real-time confidential computation.
