Decentralized AI Tokens: Unmasking the Illusion of True Autonomy


This paper critically evaluates AI-based crypto tokens, revealing their foundational reliance on centralized off-chain computation and significant scalability hurdles, challenging the perception of genuine decentralized AI.
Native Onion Routing Secures Proof-of-Stake Leader Election
PoS-CoPOR integrates native onion routing to anonymize block proposers, fundamentally preventing Denial-of-Service attacks on pre-elected leaders.
Verkle Trees: Bandwidth-Efficient Authenticated Data Structures for Scalable Blockchains


Verkle Trees introduce vector commitments into Merkle-like structures, drastically reducing proof sizes for efficient blockchain state verification and enabling scalable stateless clients.
Zero-Knowledge Proofs: Unlocking Privacy and Scalability across Digital Systems
Zero-knowledge proofs revolutionize digital trust, allowing verifiable computation without data disclosure, fundamentally enhancing privacy and scalability in diverse applications.
Publicly Verifiable Private Information Retrieval via Function Secret Sharing


This research introduces publicly verifiable private information retrieval protocols, ensuring data integrity and query privacy simultaneously for decentralized systems.
Time-Bound Schnorr Signatures Curb MEV, Restoring Transaction Predictability.


This research introduces time-bound Schnorr signatures, a cryptographic primitive that embeds an expiry block height directly into a transaction's signature, fundamentally altering MEV dynamics by restoring predictable transaction inclusion and reducing predatory extraction.
Paranoid Stateful Lambdas Enable Secure, Stateful Edge Function-as-a-Service
A new federated FaaS framework integrates cryptographically-hardened blockchains and secure enclaves, enabling robust stateful execution at the edge.
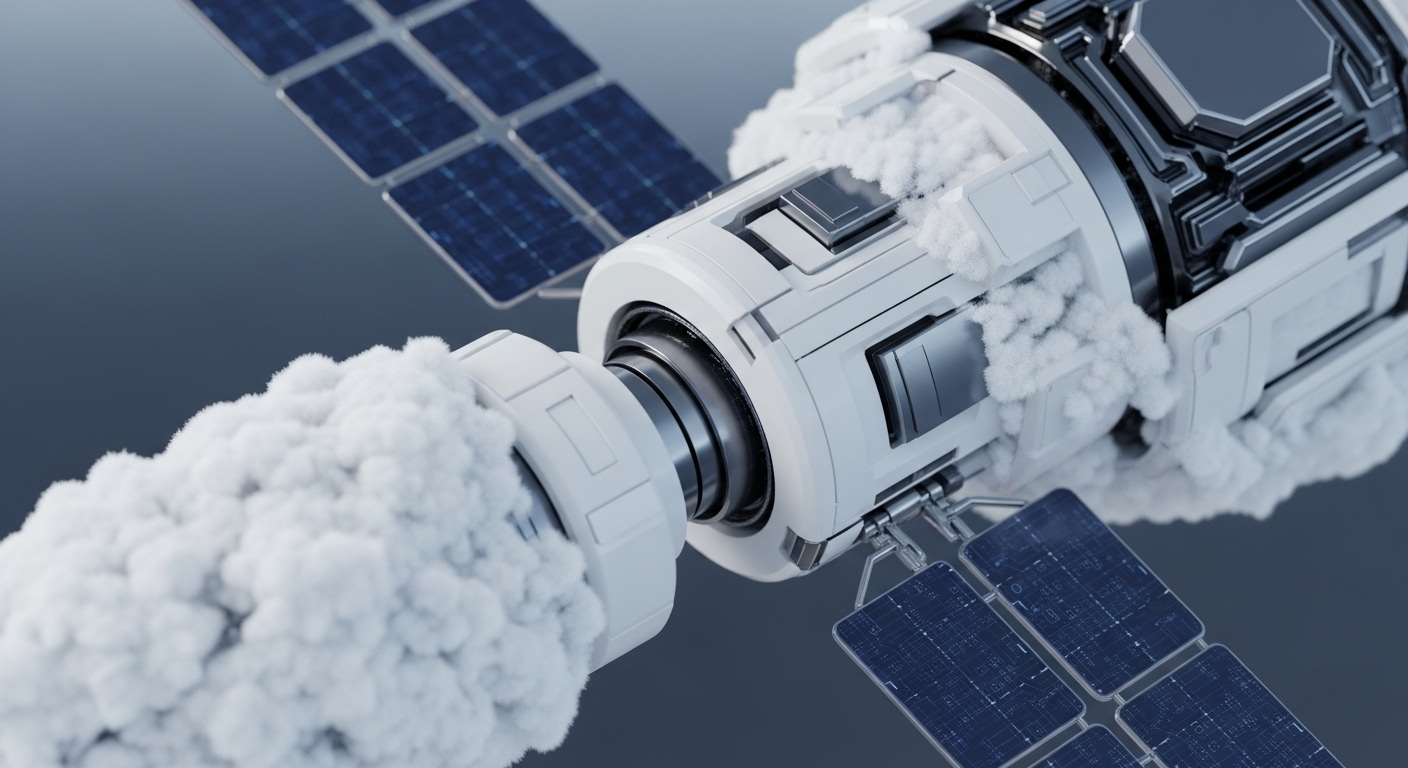
V-ZOR: Securing Cross-Chain Communication with Verifiable Oracle Relays
V-ZOR introduces a verifiable oracle relay, integrating zero-knowledge proofs and quantum-driven randomness, to fundamentally secure cross-chain data transfer and mitigate billions in risk.
Verifiable One-Time Programs Enable Open Secure Computation


This research introduces verifiable one-time programs, foundational for a novel single-round secure computation model, unlocking practical quantum-assisted cryptography with minimal resources.