Briefing
The Balancer V2 protocol suffered a catastrophic $128 million exploit, targeting its Composable Stable Pools across seven major EVM chains, including Ethereum and Arbitrum. A deep logic flaw in the core vault’s manageUserBalance function enabled the attacker to execute unauthorized internal withdrawals by impersonating legitimate users, a mechanism distinct from a flash loan attack. This event results in a significant loss of liquidity provider funds, underscoring the systemic risk inherent in complex, composable DeFi architectures; total quantifiable loss reaches approximately $128 million.

Context
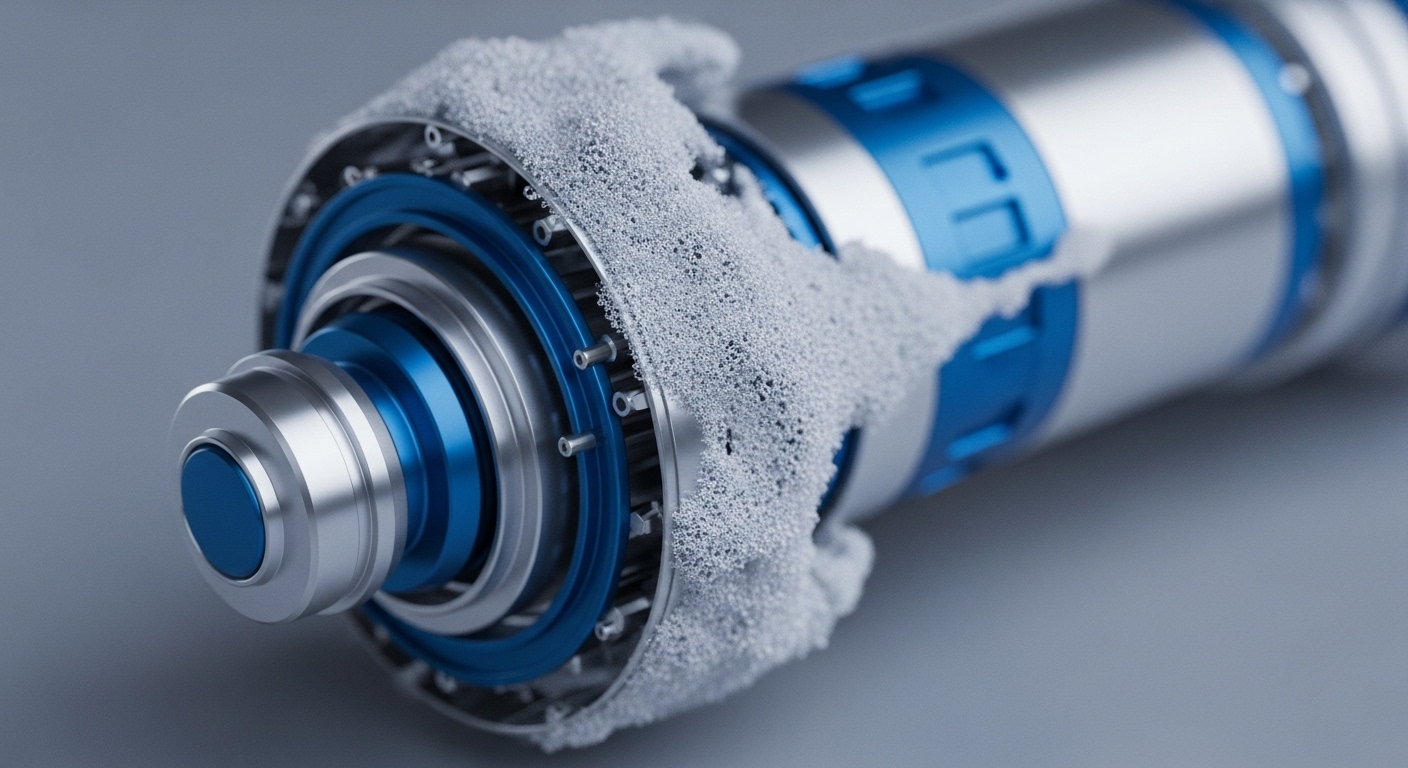
Complex DeFi vaults, managing aggregated liquidity across multiple assets and chains, present a known attack surface due to the inherent complexity of internal accounting logic. Despite multiple audits, the system contained a subtle but critical failure in access control within the V2 architecture; the contract logic did not adequately validate the true source of a withdrawal operation against the authorized user. This prior-existing class of vulnerability highlights the difficulty of fully securing contracts that manage internal balances and external calls simultaneously.

Analysis
The attack vector leveraged a specific flaw in the V2 Composable Stable Pool’s implementation of the manageUserBalance function. The vulnerability stemmed from an inadequate check on the op.sender parameter during the UserBalanceOpKind.WITHDRAW_INTERNAL operation, allowing the attacker to bypass the intended authorization logic. By crafting a malicious transaction, the attacker was able to trick the vault into processing an internal withdrawal as if it were requested by an authorized pool owner, effectively draining assets from the pools’ internal balances across the affected chains before converting the majority of the stolen funds to Ether.

Parameters
- Total Funds Drained → $128 Million – The estimated total loss across all affected chains from the exploit.
- Affected Chains → Seven EVM Blockchains – Including Ethereum, Arbitrum, Base, Optimism, Polygon, Sonic, and Berachain.
- Vulnerable Component → manageUserBalance Function – The specific smart contract function containing the faulty access control logic.
- Recovery Percentage → Approximately 15% – Funds recovered by protocols like StakeWise and Berachain through emergency measures.
Outlook
Immediate mitigation requires all users to withdraw liquidity from any remaining V2 Composable Stable Pools on affected chains, acknowledging the underlying vulnerability presents a critical risk until a complete, verified patch deploys. This event creates a heightened contagion risk for all protocols utilizing Balancer’s V2 pools or similar composable vault architectures, demanding immediate review of all integrated access control and internal accounting functions. The incident establishes new security best practices mandating formal verification of all internal balance management functions, moving beyond traditional auditing to address subtle logic flaws in highly complex DeFi primitives.
Verdict
The Balancer V2 exploit is a decisive failure of complex smart contract access control, confirming that composable DeFi architectures introduce critical, subtle logic vulnerabilities that are resistant to standard auditing practices.